
VPN Write For Us
A VPN is an organization innovation that interfaces at least one PC to a confidential organization utilizing the Web. As we made sense of in the article about what a VPN is for, organizations frequently utilize these organizations so their representatives, from their homes, lodgings, and so on, can get to corporate assets that they in any case proved unable.
However, connecting an employee’s computer to corporate resources is just one of the functions of a VPN (Virtual Private Network). So, to Write For Us, you can email us at contact@techsupportreviews.com
How to VPNWorks
When a standard device connects to the Internet, the outgoing connection communicates first with the network service provider and then with the requested site or service.
On the other hand, if the device is connected to a VPN, the path is different: The device continues to connect to the service provider first but then communicates with a VPN server. Finally, it will be from the server that the connection will be made to the site or service the device wants to access. Also, all connections that are created when a device is using a VPN are made through what is known as a VPN or data tunnel. These have various characteristics, but the most important is that they encrypt the information that travels within them, making it unreadable for those who intercept it.
So, a VPN tool modifies how devices connect to the Internet: First, it adds an intermediary to the connection and, second, the cipher in all its sections. This first feature is responsible for camouflaging the device’s original location and actual IP address since the final connection is made from the VPN server. In addition, the encryption of the entire connection makes it one of the most recommended tools for protecting network connections.
Advantages of VPN connections
- Since it is now obvious what a VPN association is and what it is going after, it is an ideal opportunity to summarize the benefits and drawbacks of utilizing this innovation.
- It works in all apps and routes all Internet traffic, unlike proxy servers, which you can only use in your web browser, and a handful of other apps that let you configure advanced connection options.
- Connects and disconnects are easily tagged. Once configured, you can activate and deactivate the connection at will.
- Additional security in WiFi access points, as long as the connection is encrypted, of course
- Fake your location. As we saw in the previous section, a VPN connection is an effective way to avoid censorship or access content limited to a particular region.
- Your Internet provider cannot know what you do on the Internet. Don’t you want your ISP to know you spend hours watching kitten videos on YouTube? With a VPN, they won’t know what you do, but beware, the company that manages it will.
When to use a VPN
There are multiple reasons why a VPN can be useful. Its main uses are:
Remote work
This tool is probably the most frequent use of VPN connections and is essential for remote work. Collaborators use them to access their organizations’ corporate networks and thus access services or sites within the same networks. In addition, by granting an encrypted connection, they are usually mandatory within those corporations that implement them, becoming a robust security tool that can prevent attacks caused, for example, by overexposure of corporate equipment abroad, as is the case of attacks on the RDP protocol.
Connections in public networks
A VPN is also often used when there is a need to access a public Wi-Fi network; that is, it does not have any credential protection. And with the increase in virtuality, accessing public networks in places like bars, cafes, coworking spaces or airports is becoming more common, both for work and leisure. However, since these networks do not have any verification, it must be a VPN tool that encrypts the connection, being protected both for those who can intercept it and for those who manage this network, who are often unknown to the user.
Censorship evasion
In countries where specific content is inaccessible or its consumption has legal consequences, VPN tools are often used to access it. This is possible thanks to the VPN server, which acts as an intermediary in the connection. Thus, network providers will not see the final destination of the connection and, therefore, will be unable to stop access to it. However, because of this feature, there are recent prohibitions on using VPNs in places where censorship is expected.
Location-based services
Not all uses of these tools are related to cybersecurity. There are services and applications, such as video games, online stores or consumption of series and movies that offer their content according to the country of origin of the connection of their users. Thanks to the change in the location of the connection, since the user’s location will actually be the location of the VPN server that acts as an intermediary, it is possible to consume content from different locations. This is also why several tools of this type offer the possibility of choosing the country or region from which the outgoing connection to the Internet is made.
In short, a VPN is useful when we have to protect a sensitive or previously insecure connection (such as a public Wi-Fi network) or when we want to hide or modify the connection’s location.
How to Submit Your Article to Tech Support Reviews?
To Write For Us, you can email at contact@techsupportreviews.com
Why Write For Us at Tech Support Reviews – VPN Write For Us
Search Terms Related to VPN Write For Us
Best VPN services
VPN reviews
VPN comparison
VPN for streaming
VPN for torrenting
Free VPN services
VPN for gaming
VPN for Netflix
VPN for Windows
VPN for Mac
VPN for Android
VPN for iOS
VPN security
VPN privacy
VPN setup
VPN download
VPN apps
VPN providers
VPN deals
VPN benefits
VPN pricing
VPN tutorial
VPN guides
VPN FAQs
VPN troubleshooting
VPN encryption
VPN for business
VPN for remote work
VPN for public Wi-Fi
VPN for online banking
Search Terms Related for VPN Write For Us
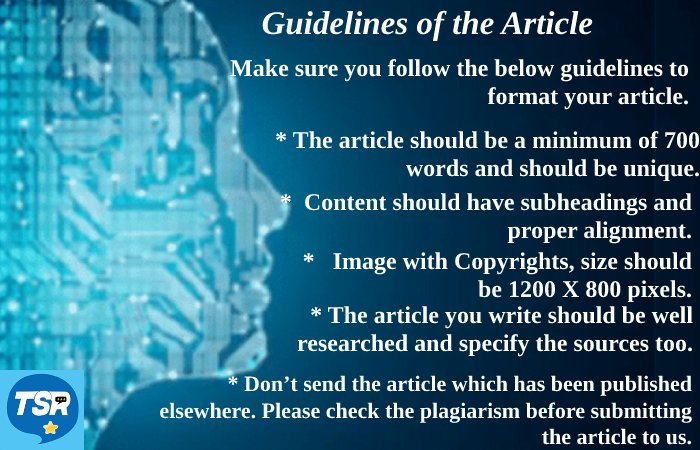
Guidelines of the Article – VPN Write For Us
To submit an article, please email us at contact@techsupportreviews.com with the subject “Guest Post for Techsupportreviews Site. Our publication team will contact you within 12 hours.

